This is the 2nd part of the EIGRP summarization series. Please read previous post if you didn't to understand the topic better. The network diagram from previous post:
Below you can see routing tables from R4, R5 and R6 before summarization:
And now we check routing tables on all devices:
I shutdown subnet 10.3.5.0/24 which is on R5 and I will check what kind of EIGRP messages I can see on R4.
Connection test before I shutdown the network:

but the response starts from TTL=255 and goes down:
This is next hop with TTL=2
and its response with TTL=254
and finally last one with TTL=4
and its response with TTL=253
I think I went to deep with the traceroute. If you are interested to read more there is a dedicated post only for traceroute and its different variations (http://myitmicroblog.blogspot.com/2015/01/traceroute-cisco-linux-and-windows.html)
Going back to our main topic: one subnet is unreachable but due to summarization no one is aware of it (except R5 of course) - this is black holing. This is one of the cons of summarization but in a huge production networks it is impossible to keep all prefixes in the routing tables. As you probably notice we also limit query range. R4 didn't receive any query as it happened in the scenario in the previous post. This is a huge pros. The number of EIGRP messages dropped significantly.
Once the failure is detected R5 sends query looking for alternate path to it but the query is not sent further behind R3 as it was in last scenario without summarization:
Capture from R3 (failure detected at 00:20:47):
and this is what I see on R2:
and R4:
What we have just proved that summarization is one of the method to limit the scope of queries, lower the number of prefixes on the routing table. In next post I will test another feature 'EIGRP stub' to achieve pretty much the same result.
Below you can see routing tables from R4, R5 and R6 before summarization:
R4#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 25 subnets, 2 masks D 10.0.0.0/24 [90/153600] via 10.2.0.2, 01:30:40, FastEthernet0/0 D 10.1.0.0/24 [90/204800] via 10.2.0.2, 00:54:52, FastEthernet0/0 D 10.1.1.0/24 [90/205440] via 10.2.0.2, 00:54:51, FastEthernet0/0 D 10.1.2.0/24 [90/205440] via 10.2.0.2, 00:54:51, FastEthernet0/0 D 10.1.3.0/24 [90/205440] via 10.2.0.2, 00:54:51, FastEthernet0/0 D 10.1.4.0/24 [90/205440] via 10.2.0.2, 00:54:51, FastEthernet0/0 D 10.1.5.0/24 [90/205440] via 10.2.0.2, 00:54:51, FastEthernet0/0 C 10.2.0.0/24 is directly connected, FastEthernet0/0 L 10.2.0.4/32 is directly connected, FastEthernet0/0 C 10.2.1.0/24 is directly connected, Loopback1 L 10.2.1.4/32 is directly connected, Loopback1 C 10.2.2.0/24 is directly connected, Loopback2 L 10.2.2.4/32 is directly connected, Loopback2 C 10.2.3.0/24 is directly connected, Loopback3 L 10.2.3.4/32 is directly connected, Loopback3 C 10.2.4.0/24 is directly connected, Loopback4 L 10.2.4.4/32 is directly connected, Loopback4 C 10.2.5.0/24 is directly connected, Loopback5 L 10.2.5.4/32 is directly connected, Loopback5 D 10.3.0.0/24 [90/204800] via 10.2.0.2, 01:24:33, FastEthernet0/0 D 10.3.1.0/24 [90/205440] via 10.2.0.2, 00:00:09, FastEthernet0/0 D 10.3.2.0/24 [90/205440] via 10.2.0.2, 00:00:09, FastEthernet0/0 D 10.3.3.0/24 [90/205440] via 10.2.0.2, 00:00:09, FastEthernet0/0 D 10.3.4.0/24 [90/205440] via 10.2.0.2, 00:00:09, FastEthernet0/0 D 10.3.5.0/24 [90/205440] via 10.2.0.2, 00:00:09, FastEthernet0/0 R4#
R5#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 25 subnets, 2 masks D 10.0.0.0/24 [90/153600] via 10.3.0.3, 01:27:47, FastEthernet0/0 D 10.1.0.0/24 [90/204800] via 10.3.0.3, 00:58:04, FastEthernet0/0 D 10.1.1.0/24 [90/205440] via 10.3.0.3, 00:58:04, FastEthernet0/0 D 10.1.2.0/24 [90/205440] via 10.3.0.3, 00:58:04, FastEthernet0/0 D 10.1.3.0/24 [90/205440] via 10.3.0.3, 00:58:03, FastEthernet0/0 D 10.1.4.0/24 [90/205440] via 10.3.0.3, 00:58:03, FastEthernet0/0 D 10.1.5.0/24 [90/205440] via 10.3.0.3, 00:58:03, FastEthernet0/0 D 10.2.0.0/24 [90/204800] via 10.3.0.3, 00:59:06, FastEthernet0/0 D 10.2.1.0/24 [90/205440] via 10.3.0.3, 00:58:32, FastEthernet0/0 D 10.2.2.0/24 [90/205440] via 10.3.0.3, 00:58:32, FastEthernet0/0 D 10.2.3.0/24 [90/205440] via 10.3.0.3, 00:58:32, FastEthernet0/0 D 10.2.4.0/24 [90/205440] via 10.3.0.3, 00:58:32, FastEthernet0/0 D 10.2.5.0/24 [90/205440] via 10.3.0.3, 00:58:32, FastEthernet0/0 C 10.3.0.0/24 is directly connected, FastEthernet0/0 L 10.3.0.5/32 is directly connected, FastEthernet0/0 C 10.3.1.0/24 is directly connected, Loopback1 L 10.3.1.5/32 is directly connected, Loopback1 C 10.3.2.0/24 is directly connected, Loopback2 L 10.3.2.5/32 is directly connected, Loopback2 C 10.3.3.0/24 is directly connected, Loopback3 L 10.3.3.5/32 is directly connected, Loopback3 C 10.3.4.0/24 is directly connected, Loopback4 L 10.3.4.5/32 is directly connected, Loopback4 C 10.3.5.0/24 is directly connected, Loopback5 L 10.3.5.5/32 is directly connected, Loopback5 R5#
R6#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 25 subnets, 2 masks D 10.0.0.0/24 [90/153600] via 10.1.0.1, 00:58:52, FastEthernet0/0 C 10.1.0.0/24 is directly connected, FastEthernet0/0 L 10.1.0.6/32 is directly connected, FastEthernet0/0 C 10.1.1.0/24 is directly connected, Loopback1 L 10.1.1.6/32 is directly connected, Loopback1 C 10.1.2.0/24 is directly connected, Loopback2 L 10.1.2.6/32 is directly connected, Loopback2 C 10.1.3.0/24 is directly connected, Loopback3 L 10.1.3.6/32 is directly connected, Loopback3 C 10.1.4.0/24 is directly connected, Loopback4 L 10.1.4.6/32 is directly connected, Loopback4 C 10.1.5.0/24 is directly connected, Loopback5 L 10.1.5.6/32 is directly connected, Loopback5 D 10.2.0.0/24 [90/204800] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.2.1.0/24 [90/205440] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.2.2.0/24 [90/205440] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.2.3.0/24 [90/205440] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.2.4.0/24 [90/205440] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.2.5.0/24 [90/205440] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.3.0.0/24 [90/204800] via 10.1.0.1, 00:58:52, FastEthernet0/0 D 10.3.1.0/24 [90/205440] via 10.1.0.1, 00:04:10, FastEthernet0/0 D 10.3.2.0/24 [90/205440] via 10.1.0.1, 00:04:10, FastEthernet0/0 D 10.3.3.0/24 [90/205440] via 10.1.0.1, 00:04:10, FastEthernet0/0 D 10.3.4.0/24 [90/205440] via 10.1.0.1, 00:04:10, FastEthernet0/0 D 10.3.5.0/24 [90/205440] via 10.1.0.1, 00:04:10, FastEthernet0/0 R6#
Now I enable summarization on all routers according to the diagram below:
And now we check routing tables on all devices:
R2#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 8 subnets, 4 masks C 10.0.0.0/24 is directly connected, FastEthernet0/0 L 10.0.0.2/32 is directly connected, FastEthernet0/0 D 10.1.0.0/16 [90/153600] via 10.0.0.1, 00:00:49, FastEthernet0/0 D 10.2.0.0/16 is a summary, 00:02:46, Null0 D 10.2.0.0/21 [90/103040] via 10.2.0.4, 00:03:25, FastEthernet1/0 C 10.2.0.0/24 is directly connected, FastEthernet1/0 L 10.2.0.2/32 is directly connected, FastEthernet1/0 D 10.3.0.0/16 [90/153600] via 10.0.0.3, 00:04:14, FastEthernet0/0 R2#
R4#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 16 subnets, 4 masks D 10.0.0.0/24 [90/153600] via 10.2.0.2, 01:43:57, FastEthernet0/0 D 10.1.0.0/16 [90/204800] via 10.2.0.2, 00:03:03, FastEthernet0/0 D 10.2.0.0/21 is a summary, 00:05:39, Null0 C 10.2.0.0/24 is directly connected, FastEthernet0/0 L 10.2.0.4/32 is directly connected, FastEthernet0/0 C 10.2.1.0/24 is directly connected, Loopback1 L 10.2.1.4/32 is directly connected, Loopback1 C 10.2.2.0/24 is directly connected, Loopback2 L 10.2.2.4/32 is directly connected, Loopback2 C 10.2.3.0/24 is directly connected, Loopback3 L 10.2.3.4/32 is directly connected, Loopback3 C 10.2.4.0/24 is directly connected, Loopback4 L 10.2.4.4/32 is directly connected, Loopback4 C 10.2.5.0/24 is directly connected, Loopback5 L 10.2.5.4/32 is directly connected, Loopback5 D 10.3.0.0/16 [90/204800] via 10.2.0.2, 00:06:28, FastEthernet0/0 R4#
R1#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 8 subnets, 4 masks C 10.0.0.0/24 is directly connected, FastEthernet0/0 L 10.0.0.1/32 is directly connected, FastEthernet0/0 D 10.1.0.0/16 is a summary, 00:05:04, Null0 D 10.1.0.0/21 [90/103040] via 10.1.0.6, 00:06:06, FastEthernet1/0 C 10.1.0.0/24 is directly connected, FastEthernet1/0 L 10.1.0.1/32 is directly connected, FastEthernet1/0 D 10.2.0.0/16 [90/153600] via 10.0.0.2, 00:07:01, FastEthernet0/0 D 10.3.0.0/16 [90/153600] via 10.0.0.3, 00:08:28, FastEthernet0/0 R1#
R6#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 16 subnets, 4 masks D 10.0.0.0/24 [90/153600] via 10.1.0.1, 01:10:56, FastEthernet0/0 D 10.1.0.0/21 is a summary, 00:06:54, Null0 C 10.1.0.0/24 is directly connected, FastEthernet0/0 L 10.1.0.6/32 is directly connected, FastEthernet0/0 C 10.1.1.0/24 is directly connected, Loopback1 L 10.1.1.6/32 is directly connected, Loopback1 C 10.1.2.0/24 is directly connected, Loopback2 L 10.1.2.6/32 is directly connected, Loopback2 C 10.1.3.0/24 is directly connected, Loopback3 L 10.1.3.6/32 is directly connected, Loopback3 C 10.1.4.0/24 is directly connected, Loopback4 L 10.1.4.6/32 is directly connected, Loopback4 C 10.1.5.0/24 is directly connected, Loopback5 L 10.1.5.6/32 is directly connected, Loopback5 D 10.2.0.0/16 [90/204800] via 10.1.0.1, 00:07:48, FastEthernet0/0 D 10.3.0.0/16 [90/204800] via 10.1.0.1, 00:09:16, FastEthernet0/0 R6#
R3#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 8 subnets, 4 masks C 10.0.0.0/24 is directly connected, FastEthernet0/0 L 10.0.0.3/32 is directly connected, FastEthernet0/0 D 10.1.0.0/16 [90/153600] via 10.0.0.1, 00:07:32, FastEthernet0/0 D 10.2.0.0/16 [90/153600] via 10.0.0.2, 00:09:29, FastEthernet0/0 D 10.3.0.0/16 is a summary, 00:10:57, Null0 D 10.3.0.0/21 [90/103040] via 10.3.0.5, 00:11:44, FastEthernet1/0 C 10.3.0.0/24 is directly connected, FastEthernet1/0 L 10.3.0.3/32 is directly connected, FastEthernet1/0 R3#
R5#sh ip route Codes: L - local, C - connected, S - static, R - RIP, M - mobile, B - BGP D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2 E1 - OSPF external type 1, E2 - OSPF external type 2 i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2 ia - IS-IS inter area, * - candidate default, U - per-user static route o - ODR, P - periodic downloaded static route, H - NHRP, l - LISP + - replicated route, % - next hop override Gateway of last resort is not set 10.0.0.0/8 is variably subnetted, 16 subnets, 4 masks D 10.0.0.0/24 [90/153600] via 10.3.0.3, 01:43:02, FastEthernet0/0 D 10.1.0.0/16 [90/204800] via 10.3.0.3, 00:08:13, FastEthernet0/0 D 10.2.0.0/16 [90/204800] via 10.3.0.3, 00:10:10, FastEthernet0/0 D 10.3.0.0/21 is a summary, 00:12:26, Null0 C 10.3.0.0/24 is directly connected, FastEthernet0/0 L 10.3.0.5/32 is directly connected, FastEthernet0/0 C 10.3.1.0/24 is directly connected, Loopback1 L 10.3.1.5/32 is directly connected, Loopback1 C 10.3.2.0/24 is directly connected, Loopback2 L 10.3.2.5/32 is directly connected, Loopback2 C 10.3.3.0/24 is directly connected, Loopback3 L 10.3.3.5/32 is directly connected, Loopback3 C 10.3.4.0/24 is directly connected, Loopback4 L 10.3.4.5/32 is directly connected, Loopback4 C 10.3.5.0/24 is directly connected, Loopback5 L 10.3.5.5/32 is directly connected, Loopback5 R5#
Now all groups of networks are presented under one prefix. What are the consequences of such summarization? Let's simulate outage on one of the networks.
I shutdown subnet 10.3.5.0/24 which is on R5 and I will check what kind of EIGRP messages I can see on R4.
Connection test before I shutdown the network:
R4#ping 10.3.5.5 source 10.2.5.4 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.3.5.5, timeout is 2 seconds: Packet sent with a source address of 10.2.5.4 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 28/36/44 ms R4# R4#traceroute 10.3.5.5 source 10.2.5.4 Type escape sequence to abort. Tracing the route to 10.3.5.5 VRF info: (vrf in name/id, vrf out name/id) 1 10.2.0.2 28 msec 16 msec 20 msec 2 10.0.0.3 28 msec 24 msec 20 msec 3 10.3.0.5 28 msec 32 msec 28 msec R4#
Now I shutdown the interface Loopback5 on R5 (10.3.5.0/24) and this is what I see on R4:
R5#conf t Enter configuration commands, one per line. End with CNTL/Z. R5(config)#int loo5 R5(config-if)#sh R5(config-if)# *Jul 21 15:43:02.195: %LINEPROTO-5-UPDOWN: Line protocol on Interface Loopback5, changed state to down *Jul 21 15:43:02.199: %LINK-5-CHANGED: Interface Loopback5, changed state to administratively down R5(config-if)#
on R4 I can't see any notification about 10.3.5.0/24 failure:
R4#
*Jul 21 15:43:01.635: EIGRP: Received HELLO on Fa0/0 - paklen 20 nbr 10.2.0.2
*Jul 21 15:43:01.635: AS 100, Flags 0x0:(NULL), Seq 0/0 interfaceQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0
*Jul 21 15:43:01.639: {type = 1, length = 12}
*Jul 21 15:43:01.639: {vector = {
*Jul 21 15:43:01.643: {01000100 0000000F}
*Jul 21 15:43:01.651: }
*Jul 21 15:43:01.651: {type = 4, length = 8}
*Jul 21 15:43:01.655: {vector = {
*Jul 21 15:43:01.655: {0B000200}
*Jul 21 15:43:01.655: }
R4#
*Jul 21 15:43:04.543: EIGRP: Sending HELLO on Fa0/0 - paklen 26
*Jul 21 15:43:04.543: AS 100, Flags 0x0:(NULL), Seq 0/0 interfaceQ 0/0 iidbQ un/rely 0/0
*Jul 21 15:43:04.547: {type = 1, length = 12}
*Jul 21 15:43:04.547: {vector = {
*Jul 21 15:43:04.547: {01000100 0000000F}
*Jul 21 15:43:04.551: }
*Jul 21 15:43:04.551: {type = 4, length = 8}
*Jul 21 15:43:04.551: {vector = {
*Jul 21 15:43:04.551: {0B000200}
*Jul 21 15:43:04.551: }
*Jul 21 15:43:04.551: {type = 6, length = 6}
*Jul 21 15:43:04.551: {vector = {
*Jul 21 15:43:04.551: {000D}
*Jul 21 15:43:04.555: }
R4#
*Jul 21 15:43:06.095: EIGRP: Received HELLO on Fa0/0 - paklen 20 nbr 10.2.0.2
*Jul 21 15:43:06.095: AS 100, Flags 0x0:(NULL), Seq 0/0 interfaceQ 0/0 iidbQ un/rely 0/0 peerQ un/rely 0/0
*Jul 21 15:43:06.095: {type = 1, length = 12}
*Jul 21 15:43:06.095: {vector = {
*Jul 21 15:43:06.095: {01000100 0000000F}
*Jul 21 15:43:06.095: }
*Jul 21 15:43:06.095: {type = 4, length = 8}
*Jul 21 15:43:06.095: {vector = {
*Jul 21 15:43:06.095: {0B000200}
*Jul 21 15:43:06.095: }
R4#
*Jul 21 15:43:08.939: EIGRP: Sending HELLO on Fa0/0 - paklen 26
*Jul 21 15:43:08.939: AS 100, Flags 0x0:(NULL), Seq 0/0 interfaceQ 0/0 iidbQ un/rely 0/0
*Jul 21 15:43:08.943: {type = 1, length = 12}
*Jul 21 15:43:08.943: {vector = {
*Jul 21 15:43:08.943: {01000100 0000000F}
*Jul 21 15:43:08.943: }
*Jul 21 15:43:08.943: {type = 4, length = 8}
*Jul 21 15:43:08.943: {vector = {
*Jul 21 15:43:08.943: {0B000200}
*Jul 21 15:43:08.943: }
*Jul 21 15:43:08.943: {type = 6, length = 6}
*Jul 21 15:43:08.943: {vector = {
*Jul 21 15:43:08.943: {000D}
*Jul 21 15:43:08.943: }
R4#
Let's test the connectivity now:
R4#ping 10.3.5.5 source 10.2.5.4 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 10.3.5.5, timeout is 2 seconds: Packet sent with a source address of 10.2.5.4 UUUUU Success rate is 0 percent (0/5) R4#
As you can see I can't reach the network:
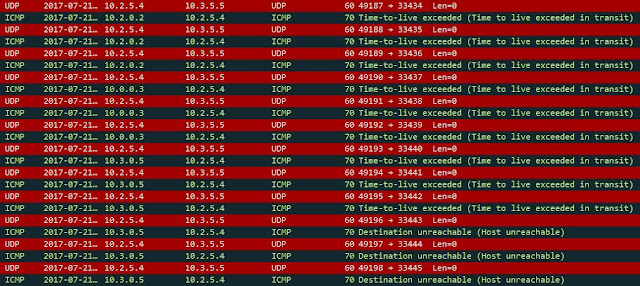
R5 sent ICMP packet - Destination unreachable (Host unreachable) - type 3, code 1:

From traceroute output you can see no response from the destination (4th hop):
R4#traceroute 10.3.5.5 source 10.2.5.4 Type escape sequence to abort. Tracing the route to 10.3.5.5 VRF info: (vrf in name/id, vrf out name/id) 1 10.2.0.2 16 msec 12 msec 8 msec 2 10.0.0.3 20 msec 20 msec 20 msec 3 10.3.0.5 40 msec 32 msec 28 msec 4 10.3.0.5 !H !H !H R4#
As you remember traceroute increases TTL by one hitting every hop in transit:
but the response starts from TTL=255 and goes down:
This is next hop with TTL=2
and its response with TTL=254
and finally last one with TTL=4
and its response with TTL=253
I think I went to deep with the traceroute. If you are interested to read more there is a dedicated post only for traceroute and its different variations (http://myitmicroblog.blogspot.com/2015/01/traceroute-cisco-linux-and-windows.html)
Going back to our main topic: one subnet is unreachable but due to summarization no one is aware of it (except R5 of course) - this is black holing. This is one of the cons of summarization but in a huge production networks it is impossible to keep all prefixes in the routing tables. As you probably notice we also limit query range. R4 didn't receive any query as it happened in the scenario in the previous post. This is a huge pros. The number of EIGRP messages dropped significantly.
Once the failure is detected R5 sends query looking for alternate path to it but the query is not sent further behind R3 as it was in last scenario without summarization:
Capture from R3 (failure detected at 00:20:47):
and this is what I see on R2:
and R4:
What we have just proved that summarization is one of the method to limit the scope of queries, lower the number of prefixes on the routing table. In next post I will test another feature 'EIGRP stub' to achieve pretty much the same result.













Comments
Post a Comment