Recently I worked on one project where a client requested to re-route web traffic to the GRE tunnel to perform traffic inspection. I would like to share with you what is required if you configure it on FortiGate.
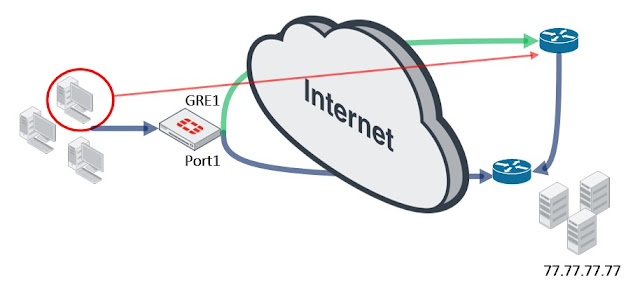
We need a new GRE interface and policy base routing (PBR) to change the route for specific source IPs. Of course you need firewall policies to permit the traffic.
Let's start with GRE interface. Unfortunately you can't configure it using the GUI, only CLI is the option:
config system gre-tunnel
edit "gre1"
set interface "port1"
set local-gw 55.55.55.55
set remote-gw 44.44.44.44
next
end
When the end peer is Cisco router, you need to set the IP for the GRE interface:
config system interface
edit gre1
set ip 192.168.10.10 255.255.255.255
set remote-ip192.168.10.20
end
In next step we need to fix routing. We need the alternate path via GRE but to keep the route in the active routing table you need to set the same AD (administrative distance) and change priority to make the path less preferred:
config router static
edit 2
set device "gre1"
set dst 0.0.0.0 0.0.0.0
set priority 10
next
end
Local-FortiGate # get router info routing-table all
Routing table for VRF=0
Codes: K - kernel, C - connected, S - static, R - RIP, B - BGP
O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default
S* 0.0.0.0/0 [10/0] via 55.55.55.254, port1
[10/0] is directly connected, gre1, [10/0]
C 10.0.1.0/24 is directly connected, port3
C 10.200.1.0/24 is directly connected, port1
Local-FortiGate #
Now, once we have the interface and routing we can add PBR, which should change the path for "LOCAL_SUBNET" and TCP/80:
config router policy
edit 1
set input-device "port3"
set srcaddr "LOCAL_SUBNET"
set dstaddr "ALL"
set protocol 6
set start-port 80
set end-port 80
set output-device "gre1"
next
end
Now you can add firewall policies, which permit traffic between LAN and GRE interfaces (not presented here). Let's do a test. ICMP is sent via port1:
id=20085 trace_id=30 func=print_pkt_detail line=5517 msg="vd-root:0 received a packet(proto=1, 10.0.1.10:1->77.77.77.77:2048) from port3. type=8, code=0, id=1, seq=165."
id=20085 trace_id=30 func=init_ip_session_common line=5682 msg="allocate a new session-0000229e"
id=20085 trace_id=30 func=iprope_dnat_check line=4942 msg="in-[port3], out-[]"
id=20085 trace_id=30 func=iprope_dnat_check line=4955 msg="result: skb_flags-02000000, vid-0, ret-no-match, act-accept, flag-00000000"
id=20085 trace_id=30 func=vf_ip_route_input_common line=2591 msg="find a route: flag=04000000 gw-55.55.55.254 via port1"
id=20085 trace_id=30 func=iprope_fwd_check line=726 msg="in-[port3], out-[port1], skb_flags-02000000, vid-0, app_id: 0, url_cat_id: 0"
and TCP via GRE:
id=20085 trace_id=31 func=print_pkt_detail line=5517 msg="vd-root:0 received a packet(proto=6, 10.0.1.10:50731->77.77.77.77:80) from port3. flag [S], seq 2551198907, ack 0, win 8192"
id=20085 trace_id=31 func=init_ip_session_common line=5682 msg="allocate a new session-000022b0"
id=20085 trace_id=31 func=iprope_dnat_check line=4942 msg="in-[port3], out-[]"
id=20085 trace_id=31 func=iprope_dnat_check line=4955 msg="result: skb_flags-02000000, vid-0, ret-no-match, act-accept, flag-00000000"
id=20085 trace_id=31 func=vf_ip_route_input_common line=2578 msg="Match policy routing: to 77.77.77.77 via ifindex-20"
id=20085 trace_id=31 func=vf_ip_route_input_common line=2591 msg="find a route: flag=04000000 gw-77.77.77.77 via gre1"
id=20085 trace_id=31 func=iprope_fwd_check line=726 msg="in-[port3], out-[gre1], skb_flags-02000000, vid-0, app_id: 0, url_cat_id: 0"
I decided to write the post about GRE and PBR because these topics are not part of NSE4 official training.
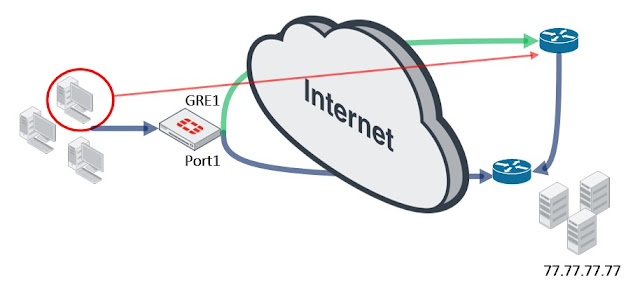
We need a new GRE interface and policy base routing (PBR) to change the route for specific source IPs. Of course you need firewall policies to permit the traffic.
Let's start with GRE interface. Unfortunately you can't configure it using the GUI, only CLI is the option:
config system gre-tunnel
edit "gre1"
set interface "port1"
set local-gw 55.55.55.55
set remote-gw 44.44.44.44
next
end
When the end peer is Cisco router, you need to set the IP for the GRE interface:
config system interface
edit gre1
set ip 192.168.10.10 255.255.255.255
set remote-ip192.168.10.20
end
In next step we need to fix routing. We need the alternate path via GRE but to keep the route in the active routing table you need to set the same AD (administrative distance) and change priority to make the path less preferred:
config router static
edit 2
set device "gre1"
set dst 0.0.0.0 0.0.0.0
set priority 10
next
end
Local-FortiGate # get router info routing-table all
Routing table for VRF=0
Codes: K - kernel, C - connected, S - static, R - RIP, B - BGP
O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default
S* 0.0.0.0/0 [10/0] via 55.55.55.254, port1
[10/0] is directly connected, gre1, [10/0]
C 10.0.1.0/24 is directly connected, port3
C 10.200.1.0/24 is directly connected, port1
Local-FortiGate #
Now, once we have the interface and routing we can add PBR, which should change the path for "LOCAL_SUBNET" and TCP/80:
config router policy
edit 1
set input-device "port3"
set srcaddr "LOCAL_SUBNET"
set dstaddr "ALL"
set protocol 6
set start-port 80
set end-port 80
set output-device "gre1"
next
end
Now you can add firewall policies, which permit traffic between LAN and GRE interfaces (not presented here). Let's do a test. ICMP is sent via port1:
id=20085 trace_id=30 func=print_pkt_detail line=5517 msg="vd-root:0 received a packet(proto=1, 10.0.1.10:1->77.77.77.77:2048) from port3. type=8, code=0, id=1, seq=165."
id=20085 trace_id=30 func=init_ip_session_common line=5682 msg="allocate a new session-0000229e"
id=20085 trace_id=30 func=iprope_dnat_check line=4942 msg="in-[port3], out-[]"
id=20085 trace_id=30 func=iprope_dnat_check line=4955 msg="result: skb_flags-02000000, vid-0, ret-no-match, act-accept, flag-00000000"
id=20085 trace_id=30 func=vf_ip_route_input_common line=2591 msg="find a route: flag=04000000 gw-55.55.55.254 via port1"
id=20085 trace_id=30 func=iprope_fwd_check line=726 msg="in-[port3], out-[port1], skb_flags-02000000, vid-0, app_id: 0, url_cat_id: 0"
and TCP via GRE:
id=20085 trace_id=31 func=print_pkt_detail line=5517 msg="vd-root:0 received a packet(proto=6, 10.0.1.10:50731->77.77.77.77:80) from port3. flag [S], seq 2551198907, ack 0, win 8192"
id=20085 trace_id=31 func=init_ip_session_common line=5682 msg="allocate a new session-000022b0"
id=20085 trace_id=31 func=iprope_dnat_check line=4942 msg="in-[port3], out-[]"
id=20085 trace_id=31 func=iprope_dnat_check line=4955 msg="result: skb_flags-02000000, vid-0, ret-no-match, act-accept, flag-00000000"
id=20085 trace_id=31 func=vf_ip_route_input_common line=2578 msg="Match policy routing: to 77.77.77.77 via ifindex-20"
id=20085 trace_id=31 func=vf_ip_route_input_common line=2591 msg="find a route: flag=04000000 gw-77.77.77.77 via gre1"
id=20085 trace_id=31 func=iprope_fwd_check line=726 msg="in-[port3], out-[gre1], skb_flags-02000000, vid-0, app_id: 0, url_cat_id: 0"
I decided to write the post about GRE and PBR because these topics are not part of NSE4 official training.
Comments
Post a Comment